The security organization Shadowserver found out in a portscan of all possible 4.3 billion IPv4 addresses in June 2020 that about 80,000 unsecured printers can be addressed via Internet Printing Protocol (IPP) support. IPP allows attackers to obtain a range of information from openly communicating printers over the Internet, including the firmware version, standard, and WLAN SSID.
Based on the information obtained, hackers can exploit possible security gaps (exploits) and thus use the printers as a gateway into company networks. The command IPP Get-Printer Attributes on TCP port 631 was used for the port scan. According to Speedguide, this command can also be misused for a denial of service attack (DoS) on the MacOS printer sharing service.
Remote printing via IPP
IPP was developed to start and stop printer jobs outside the local network and to query the status of printers. Actually, the encryption and authentication via TLS should prevent third parties from reading out information. IPP is also compatible with the encrypted Internet protocol HTTPS.
According to the shadow server, the scanned printers are vulnerable because the existing security functions were not configured correctly. Even a firewall, which offers further protection, was only used in rare cases for the detected printers.
South Korea on place one
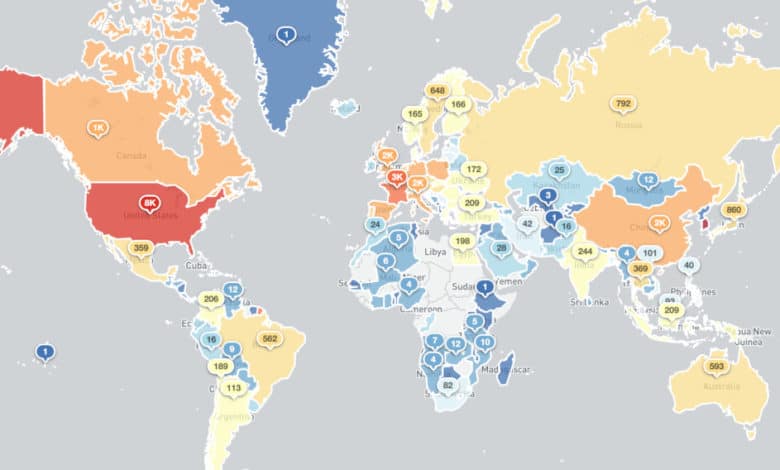
According to the Binaryedge search engine, there are about 700,000 IPP printers with Internet connection worldwide. The current report thus shows that about 11.5 percent of all IPP printers are incorrectly configured. South Korea alone accounts for 36,300 of the approximately 70,000 insecure printers, 7,900 printers are in the U.S.A. and 6,700 printers in Taiwan. Germany is in tenth place.
The high proportion of unsafe printers in South Korea is due to the fact that a particularly large number of Samsung models are affected, which sell significantly more devices in their home country than their foreign competitors.



