Members of the Chaos Computer Club have succeeded in using comparatively simple means to deceive in the videoident procedure. As a result, health insurers are now prohibited from continuing to use the procedure to check access to electronic medical records.
Videoident procedure increasingly popular
The video identity procedure is designed to verify a person’s identity during a video chat. For this purpose, a connection is established to a service provider, to whom one’s own ID card must be presented in the video chat. The ID is checked for security features and the photo on the ID is compared with the person seen in the video chat. This procedure is being used by more and more companies. For example, it is the standard identification procedure at numerous online banks, as well as at health insurance companies, mobile phone providers and online casinos. Anyone who wants to open an account today no longer has to visit a bank branch in person, but can sit in front of their own PC. Weaknesses in this identification system are highly problematic due to its use in numerous sensitive areas: accounts can be opened under false names, access to other people’s medical records is possible, etc.
Accounts can be opened under false identities with little effort
Members of the Chaos Computer Club led by security researcher Martin Tschirsich have now proven that it is possible to pass the video identity test with a false identity with relatively little effort. To do this, they took photographs of an ID card from a wide variety of angles and then created a digital clone in which important data from the document was exchanged. This made it possible to create a video in which the forged ID card was shown from a wide variety of perspectives – and thus with all its visual characteristics.
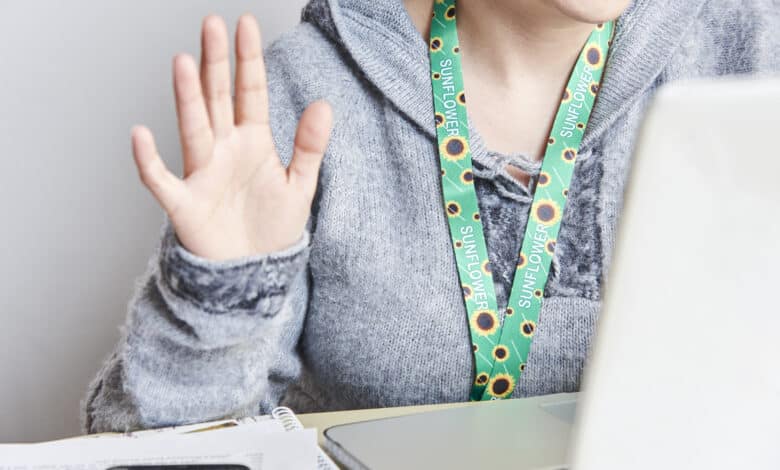
Another common test in the video ID process is to cover parts of the ID with a finger. In this way, video manipulations like those of the Chaos Computer Club are supposed to stand out in the examination interview. But Tschirsich’s team also cleared this hurdle. It resorted to a technique that can recognize and distinguish objects and thus separate different video layers. In addition to this technique – which is included in conventional video editing software – it needed red paint. Since object recognition has difficulty correctly detecting object boundaries when objects look similar, the subject painted her hand red. This made it easier for the technology to detect the boundaries of the hand and the ID document, and thus to make a correct layer separation in the video. This also allowed the overlapping of individual ID elements with the finger to be implemented.
The final tool used by the Chaos Computer Club was a television. A video of the forged document, manipulated in real time, was played through it. The cell phone camera was used to film the television during the test interview. The employees of the testing services did not notice that they were not communicating with a person sitting directly in front of the camera. A total of six providers in the video testing were deceived in this way. It is not clear from the published documents how many providers were tested.
Gaining access to sensitive data
In the test, Tschirsich’s team gained access to numerous sensitive data. As a result of the video identification, for example, it was possible to access the electronic medical records of an initiated person. In the course of the test, it also became apparent that one provider also had access to the data of other customers – which represents a serious security gap.
After the test, Tschirsich and his team requested the stored video recordings from the providers and analyzed them. In the process, they noticed several weaknesses in their own video manipulation that had not been criticized by the test subjects. Discrepancies between the data shown in the hologram and the data that could be openly read on the ID card, which could be seen in the videos, were also not noticed in the test.
Health insurers must not continue to use video ID procedures
Tschirsich subsequently demanded that the videoident procedure should not continue to be used in sensitive areas, saying, “In light of these discoveries, it would be negligent to continue to rely on videoident where misuse could potentially cause irreparable damage – for example, through unauthorized disclosure of intimate health data.” He also called for mandatory audits of companies offering the video ID process: “It’s time for an end to the reversal of the burden of proof: It shouldn’t be the data subjects who have to prove weaknesses in the systems, but rather the process operators who should be required to prove their security according to recognized rules. In the future, compliance with existing and new requirements should be regularly proven by independent tests under real attack conditions. In particular, any statement on the effectiveness of countermeasures must be based on reliable evidence. Simply claiming that some AI has been sprinkled on top of it should no longer be sufficient.”
In fact, Gematik, which is responsible for electronic health records as well as for the E-prescription, has already responded. Health insurance companies are no longer allowed to use the videoident procedure as part of accessing electronic records. The IT industry association Bitkom, however, does not agree with this ban. Managing director Bernhard Rohleder made the following comments: “With the blanket and unannounced ban on video identification procedures at health insurance companies, Gematik has done a disservice to patients in Germany.” Instead, Rohleder called for better technical safeguards for the procedure. Tschirsich, however, believes that this is difficult to achieve: “The use of AI, which is seen in the industry as a cure for most security problems, is a dead end in his opinion – and his test, which has now taken place, is a strong argument, since AI is already being used today with the promise of comprehensive security in video ID procedures.




No replies yet
Neue Antworten laden...
Gehört zum Inventar
Beteilige dich an der Diskussion in der Basic Tutorials Community →