Mike Grover’s OMG Cable looks like a standard USB-C to Lightning cable spy. However, the hacker’s new cable is capable of performing keystrokes from PCs and Macs and sending content via Wi-Fi hotspot.
Hacker wants to prove insecurity
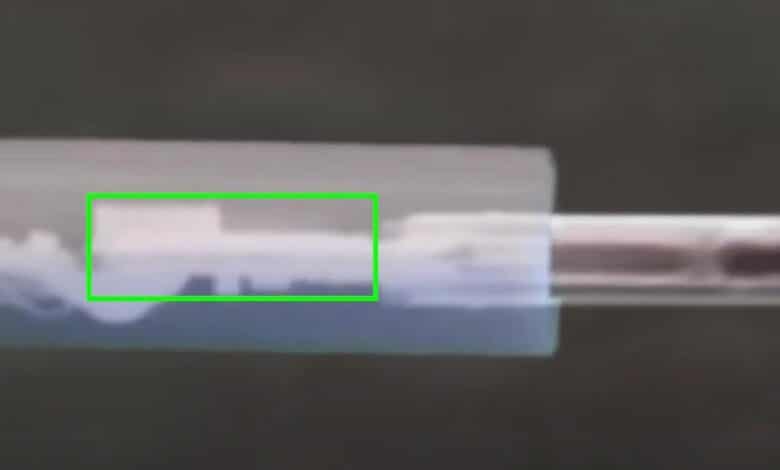
Mike Grover’s OMG Cable is like two peas in a pod to Apple’s regular white USB-C-to-Lightning cable. However, there is a huge difference inside, because it contains electronics that are capable of executing keystrokes with subsequent keylogging as well as directly forwarding the data via WLAN hotspot.
In addition, the cable has a kill switch so that the attacker is not detected. By default, this is supposed to enable attacks on Macs, PCs, iPhones and iPads.
Speaking to IT blog Motherboard, Grover said there had been people who believed USB-C cables were protected from such a form of chip insertion because of their small size, to whom he had to “show that’s not true,” Grober is quoted as saying.
The original version of the OMG Cable was a USB-A-to-Lightning cable that Hacker unveiled at the 2019 DEF CON hacking conference, after which it went into mass production. Due to the USB-A connector, there was correspondingly more space available for the necessary technology.




No replies yet
Neue Antworten laden...
Neues Mitglied
Beteilige dich an der Diskussion in der Basic Tutorials Community →