The UEFI Secure Boot feature is supposed to prevent malware from executing dangerous code during the boot process and has been an important cornerstone in cybersecurity since the late 2000s. However, over 300 MSI motherboards are said to have a flawed Secure Boot implementation, allowing almost any boot image to be loaded.
Over 300 MSI mainboards with flawed Secure Boot implementation
As an IT student and cybersecurity researcher from New Zealand named Dawid Potocki found out, over 300 MSI mainboards are equipped with a faulty Secure Boot implementation in certain versions of the UEFI firmware. However, UEFI firmware versions that were released as beta are said to be most affected.
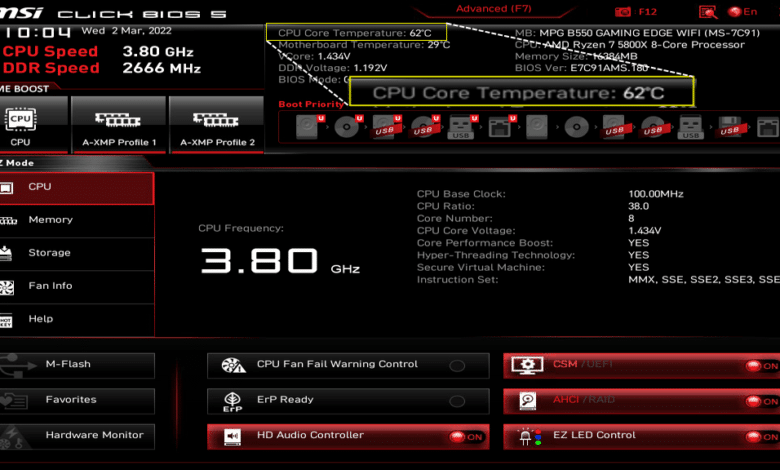
Postocki came across the bug when his MSI PRO Z790-A WiFi motherboard failed to verify cryptographic signatures at boot, according to a report from TechPowerUp. He found that his firmware accepted any boot image, no matter if it was trusted or not.
Investigations revealed that around 300 other motherboards from the manufacturer MSI had this error. Notebooks from the manufacturer, however, are not said to be affected, only motherboards designed for desktop PCs.
Did MSI know about this?
Affected motherboards are said to have an “always run” policy for Secure Boot in the process, rendering the mechanism useless. He assumes that on the part of the manufacturer, they probably knew that Microsoft would not agree to this and/or that they wanted to receive fewer tickets about Secure Boot issues for their users.
Potocki reportedly tried to contact MSI himself and share the knowledge he gained, but was unsuccessful. The full list of affected motherboards and more details were published by the IT student on Github.




No replies yet
Neue Antworten laden...
Gehört zum Inventar
Beteilige dich an der Diskussion in der Basic Tutorials Community →